Cybersecurity

5 BYOD Challenges & Solutions For Mitigating Associated Risks
BYOD, or Bring Your Own Device, is a double-edged sword that increases work productivity while putting businesses at risk of exposing confidential and sensitive data. BYOD was born out of the increasing prevalence of personal mobile devices, such as smartphones and tablets, in the workplace.

Top 10 Network Security Audit Tools in 2024: Based on 4,000 Reviews
Network security statistics show that the average data breach cost was ~$4 million in 2023. With the cost of security threats increasing, securing your company from the most common cyber attack vectors has never been more important.

Top 10 Cloud Security Tools in 2024
Cloud growth continues with domains like the cloud storage market expected to grow ~3x from 2023 to 2029. With the majority of enterprises relying mostly on the cloud, cloud security is almost synonymous with cybersecurity. Therefore cloud security includes a broad range of categories.
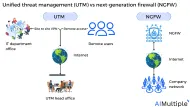
UTM vs NGFW in 2024: Which One to Choose?
Figure 1: Unified threat management (UTM) vs next-generation firewalls (NGFW) Network security is imperative for all organizations since 45% of experts see cyber incidents as the most feared source of commercial interruption.

Phishing vs Whaling in 2024: 6 Key Differences
Phishing attacks are rising, and there’s no sign they’ll stop anytime soon. In 2023, ~300,000 phishing attack incidents were reported to the Internet Crime Complaint Center (IC3) in the U.S., with a 100+% increase compared to the incidents reported (114, 702) in 2019.
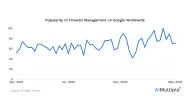
Firewall Management: Challenges and 8 Best Practices in 2024
Firewalls are the cornerstone of network security, acting as gatekeepers that regulate traffic and protect against cyber threats. Effective firewall management is crucial for maintaining a resilient network security. This article analyzes various aspects of firewall management, including the importance, key components, and best practices.

Firewall Audit Logs: Analysis and 6 Steps for Improvement in 2024
Firewall logging is essential for monitoring, analyzing, and auditing network traffic to detect potential security threats and attacks at an early stage. In the realm of cybersecurity, the management and analysis of firewall audit logs play a pivotal role in fortifying network defenses and upholding regulatory standards.

Key Components of Firewall Compliance: Guidance in 2024
The anticipated cost of cyber attacks globally was projected to reach nearly $10 trillion in 2024. The average worldwide cost of a data breach is ~$5 million. To avoid these costs, ensuring robust network security is paramount for organizations. Conducting comprehensive firewall audits is one of the cornerstone strategies for fortifying network security.

Top 4 Microsoft System Center Alternatives in 2024
Network security statistics show that data breaches exposed over 6 million data records globally during the first quarter of 2023. Companies that deal with complex security rules and firewall assessment methods, each with different requirements, may find it difficult to manage network security policies that will prevent the IT environment from data breaches.

Top 8 Next-Generation Firewall (NGFW) Features in 2024
The network security statistics show that the number of incidents in North America increased from 23% of all cases in 2021 to 25% in 2022. The U.S. accounted for 80% of the North American region’s cybercrime. Recent security incidents in the U.S.