The importance of proxy servers extends across multiple industries, including finance, marketing, and HR. By acting as intermediaries between the client and the targeted web server, they offer numerous benefits, from efficient data collection to enhancing online privacy.
Moreover, it is important to note that not all proxy server types provide the same benefits. Understanding the specific requirements of the use case is essential for choosing the right proxy service. This article explores the top applications of proxy services across different industries and departments.
Marketing
1. Competitive analysis
Competitive analysis, also known as competitor analysis, is the process of identifying and evaluating competitors to gain insights into their strengths and weaknesses. Proxies help companies conduct competitive analysis by gathering information about their pricing strategy, market share, and customer reviews.
Data gathering is an essential step of competitive analysis. This could be product descriptions, customer review data, or pricing information. First, you need to identify who your competitors are and then gather information about them. After gathering information from competitors’ websites, the next step is to analyze the collected data.
There are various tools for web scraping, including no-code web scraping tools (for those without knowledge of programming), web scraping APIs (for more tailored needs), or in-house web scrapers (provide full control over data scraping projects).
Many eCommerce websites employ anti-scraping measures to prevent automated data collection activities, making proxies crucial in competitive analysis. Proxy servers enable users to bypass anti-bot measures such as rate limiting, IP bans, and CAPTCHAs.
Sponsored
Bright Data’s Web Scraper IDE enables businesses and individuals to build their web scrapers in a JavaScript coding environment. The IDE includes unblocking technologies, such as built-in proxy server, to bypass CAPTCHAs and IP blocks. It offers ready-made JavaScript functions and code templated from major websites.
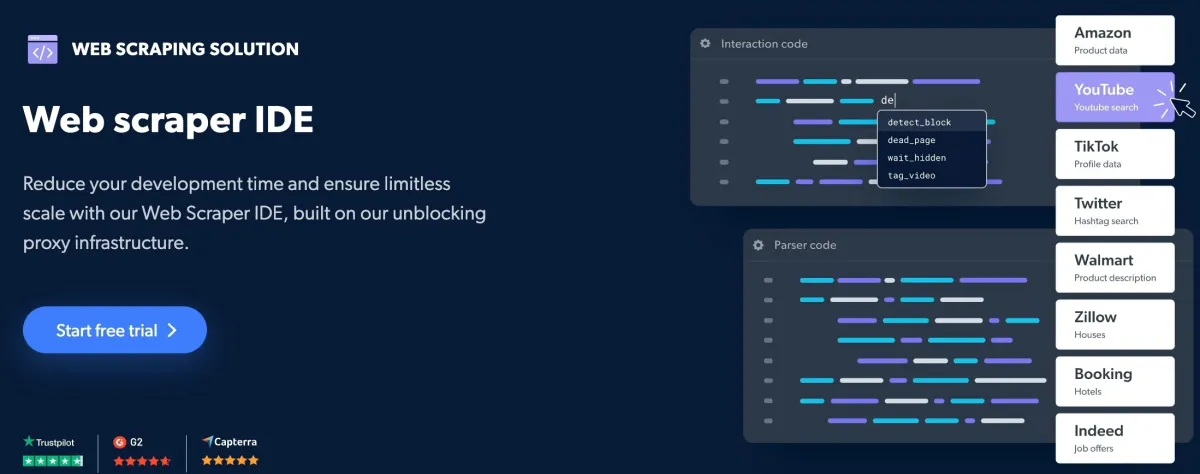
Source: Bright Data
2. SEO monitoring
SEO rankings can vary by location to provide the most relevant results to users. For example, the IP address of the user can influence the search results.
For example, if someone in Canada searches for “best pizza place”, the search engine will prioritize local business listings and show pizza places in Canada.
Proxies allow users to simulate searches from different locations and monitor how their websites rank for target keywords in different geographical locations.
3. Ad verification
Proxies help businesses ensure that digital ad campaigns are displayed as intended on the desired location to the desired audience. Advertisers can use proxy servers located in target areas to conduct location-based checks.
If your company runs ad campaigns on multiple websites at the same time, it would be time-consuming to audit every single ad. You can leverage rotating proxy servers, such as rotating residential proxies, to verify ads at scale without being detected and blocked by the target website.
4. Social media management
Managing multiple social media accounts pose several challenges, such as geographical barriers, rate limiting, account creation, and data privacy. For example, managing multiple social media accounts for different clients from the same device can lead to IP tracking and suspension due to suspicious activity.
Rotating proxies can distribute connection requests across multiple IP addresses, allowing you to associate each social media platform with a unique IP.
5. Pricing intelligence
Pricing intelligence is the process of extracting and analyzing pricing data. It enables businesses to apply dynamic pricing by monitoring the competitor prices in real-time.
Most no-code web scrapers include built-in integration with proxy services to provide a layer of anonymity during the web scraping process. By mimicking real users from different locations, proxies can collect more accurate data without getting restricted by website limitations.
6. Brand protection
There are different types of brand infringement, such as counterfeiting, copyright infringement, design infringement, and patent infringement. Using web scraping tools integrated with proxies allows brands to identify unauthorized sellers.
Web scrapers scan the web to collect information about products similar to the brand’s own products. By assigning an IP address from the target location, proxies enable brands to access geo-restricted content and identify region-specific unauthorized sellers.
Sales
6. Lead generation
Web scraping helps sales teams expand their customer base with web data. For instance, you can use LinkedIn scraping tools to crawl public profiles and extract data from the platform, such as user profiles, job listings, and company information. The collected data allows sales teams to generate more personalized and targeted sales pitches.
It is important to employ web scraping techniques responsibly and comply with the target website’s Terms of Service. Scraping LinkedIn periodically to have up-to-date lists of people can result in an IP ban. Proxies make it appear as though your requests are coming from different locations, helping you avoid detection and IP bans.
7. Regional pricing strategies
Prices can be set based on fluctuating exchange rates, demand in a specific region, or logistical issues. Businesses must conduct ongoing market research to ensure that their pricing strategy is in line with local conditions.
Web scrapers help them collect pricing data from competitors’ websites in different regions. You can integrate proxy services with scrapers to gather data anonymously.
The integration of web scrapers and proxies reduces the risk of being detected and blocked, allowing for continuous data collection.
8. Social media outreach
When you need to contact a large number of accounts, volume and scalability can be time-consuming and resource-intensive. Aggressive outreach attempts could lead to account suspensions. Residential proxies assign users real IP addresses from ISPs, making them more legitimate. You can use residential IPs from specific regions or countries to achieve a higher level of anonymity.
Human resources (HR)
9. Fetching candidate data
Fetching candidate data is the process of collecting information about job applicants, including social media profiles and resumes. It can be done manually or with the use of automated tools. Large-scale web scraping is challenging using manual web scraping techniques.
On the other hand, automated tools such as social media scrapers can pose ethical and legal challenges. Collecting data using different IP addresses reduces the likelihood of being flagged as automated activity by the website you are scraping from.
Research and development
10. Fetching product data
It refers to the process of extracting product data such as descriptions, images, ratings, and customer reviews from e-commerce websites. The extracted product data allows businesses to understand market trends, consumer preferences, and build a new product. Using automated data collection techniques like custom web scrapers or web scraping APIs is the most efficient way to gather large amounts of data.
However, there are many challenges in large-scale product data scraping. For example, the website you are collecting data from may change its layout and design, which can break your web scraper. The target website may employ AJAX loading to prevent automated scraping. You can utilize datacenter or residential proxies to change IP addresses after each request or after a predetermined period.
Finance and accounting
11. Data scraping
The finance sector relies on data scraping to obtain different financial industry data points like stock market data, alternative data, news data.
For example, most public companies publish their financial data. Web scrapers can collect details about a company’s financial status to predict its ability to pay back a debt and forecast the likelihood of a debtor defaulting.
Some web scrapers include integrated proxies, enabling businesses to analyze the financial market in a specific region and adjust their financial strategies accordingly.
Data security
12. Cybersecurity
Companies can use proxies to monitor and control employee internet access. They can blocking specific content types, preventing accidental downloads of malware. Proxy servers add an extra layer of protection between the user’s device and the target web server, making it harder for websites to track a user’s activities and prevent sensitive data from leaving the organization without user authorization.
13. OSINT (Open Source Intelligence)
Open Source Intelligence (OSINT) is the process of collecting and analyzing publicly available data to support decision-making. OSINT involves extracting data from public sources such as social media platforms, blogs and websites.
Proxy servers play an essential role in OSINT collection. Using proxy servers can mask the user’s origin IP, allowing users to access geographically restricted content and bypass limits on the number of requests that can be taken within a certain timeframe.
14. Digital forensics
Digital Forensics refers to the process of investigating and analyzing data stored electronically. The aim is to preserve, identify, and extract digital artifacts legally to detect and prevent any crime.
Digital forensics includes several sub-domains such as computer, network, database, and malware forensics. Proxies allow forensic experts to prevent potential targets from identifying their real IP addresses.
You can use proxy servers to capture and archive web traffic. If the original content changes or gets deleted over time, you can still have access to the exact content.
What is a proxy server?
Proxies or proxy servers are intermediaries that act as a gateway between the client and the target website. They receive client requests, forward them to the target web server, and return the server’s response to the client.
What are the different types of proxies?
1- Datacenter proxies
Datacenter proxies are a type of proxy server hosted in data centers and cloud hosting services rather than affiliated with an Internet Service Provider (ISP). Since they are not associated with an ISP, they can be easily detected and blacklisted by websites. Datacenter Proxies are known for their speed as they use IP addresses that are sourced from a remote cloud server.
2- Residential proxies
Residential proxies use real IP addresses provided by Internet Service Providers (ISPs). Since these IP addresses are linked to real devices owned by people, they are harder to blacklist than data center proxies.
3- Mobile proxies
A mobile proxy accepts and forwards connection requests through a mobile device connection, such as a smartphone or tablet. Mobile proxies are 3G/4G/5G connections assigned to users by mobile operators. They contain real IP addresses provided by Internet Service Providers (ISPs), similar to residential proxies.
4- HTTP proxies
There are two main protocols used by proxies: HTTP and SOCKS protocols. An HTTP proxy, or HTTP tunnel, is an intermediary receiving and forwarding requests between a client browser and the destination web server in HTTP format.
5- SOCKS proxies
SOCKS, which stands for Socket Secure, is an internet protocol that monitors and manages network traffic through a proxy server between the client and the web server. Unlike an HTTP proxy that can only handle HTTP connections, SOCKS proxies are compatible with any network protocol, including HTTP, HTTPS, and SMTP.
6- Forward proxies
A forward proxy is an intermediary between clients and target servers positioned in front of clients. The most common types of forward proxies are datacenter and residential proxies. Unlike reverse proxies, forward proxies receive requests from clients and validate those requests before forwarding them to the target web server.
7- Reverse proxies
A reverse proxy sits between the client and back-end web servers to ensure the security of incoming data before forwarding them to the appropriate server. Reverse proxies can distribute incoming client requests across multiple website back-end servers to prevent any one server from becoming overloaded.
For more on proxies
- Proxy Pricing Benchmark: Lowest Price Proxy Services
- Top 7 Proxy Providers: Pricing & Features Compared
- The Ultimate Guide to Proxy Server Types
For guidance to choose the right tool, check out our sortable/filterable list of proxy service/server. and reach out to us:

Comments
Your email address will not be published. All fields are required.