Proxies help in masking your IP address and providing security against attacks on the internet. In this article, we will explore reverse proxies.
What is a reverse proxy?
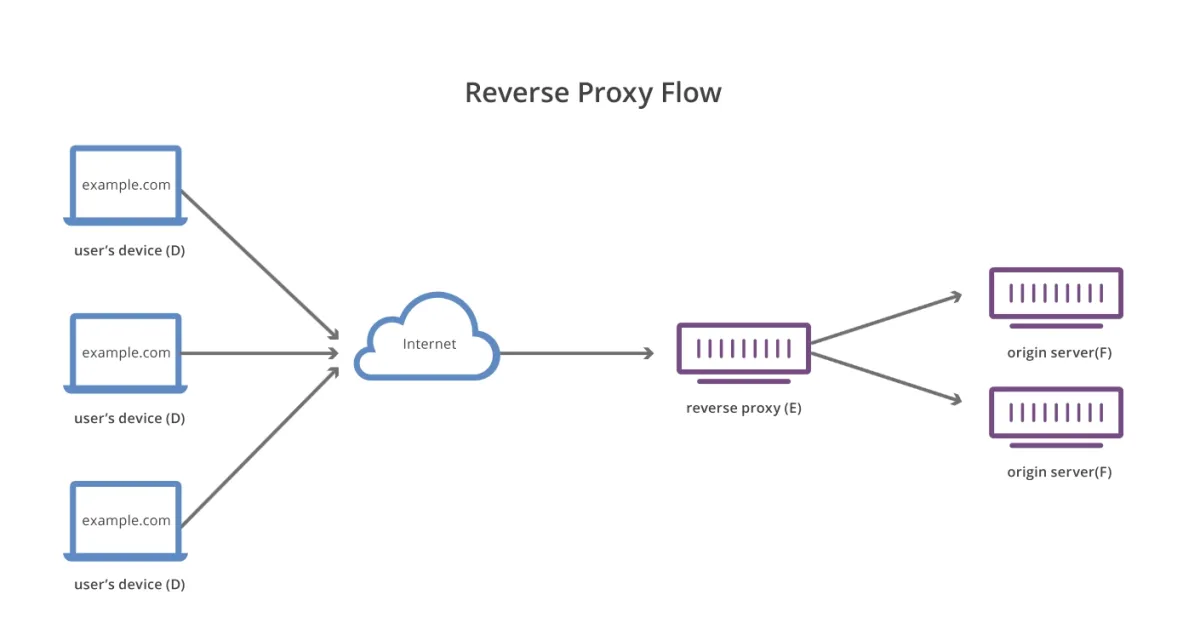
A reverse proxy is a server that sits in front of web servers. It forwards clients’ requests, like web browsers, to those servers. It is different from forward proxy, where the proxy sits in front of the clients. Reverse proxy ensures that no client ever communicates directly with the web server.
All the requests from the user’s device would go to the internet and then go to the reverse proxy server before reaching the client’s web server. The web server then sends information to the proxy server which uses the internet to send it back to the client’s user device.
What are some risks of using reverse proxies?
Though it provides security, there are some risks involved with using reverse proxies as well:
- Risk of information stored: Since a reverse proxy can track IP addresses and encrypt/decrypt information, it is also able to store data such as passwords. This can be a problem if it’s run by a malicious party. Moreover, with such sensitive information it can be risky using a reverse proxy of a third party as they need to adhere to the triad of Confidentiality, Integrity and Availability.
- HTTP request smuggling: This is a web application attack that exploits differences between web servers and their reverse proxies. It can allow the attacker to submit a request with a user’s session and interfere with the processing of HTTP requests.
- Risk of failure: If the proxy is fronting many different domains, its outage can bring down all of those. Also, if there is no way to access the back-end server directly, the outage can disrupt operations.
What are the benefits of using reverse proxies?
Just like using any proxy, using reverse proxies also has several benefits:
- Encryption tool: Encryption can be expensive for an origin server but using reverse proxies can help with this. They can decrypt all incoming requests and encrypt all outgoing requests (SSL/TSL).
- Caching: Reverse proxies can also cache content improving the performance speed, reducing page load times and improving content delivery to clients.
- Load balancing: Reverse proxies can help with the traffic flow on the main server. They can reduce the load on the main server by evenly distributing the load on all the servers. These proxies will also send clients to the servers which are located nearest to them, reducing response times.
- Security: Your origin server’s IP address is masked which provides protection against potential attacks, such as DDoS attacks. You can also place a web application firewall on your reverse proxies for further protection against hackers and bots.
- Testing: Reverse proxies can perform A/B testing and multivariate testing without JavaScript tags or coding.
Further reading
- The Ultimate Guide to Proxy Server Types
- Using Proxies for Web Scraping: How-to, Types, Best Practices
If you have any questions about how to choose a reverse proxy service that is suitable for your specific application, feel free to read our data-driven whitepaper on the topic:
You can also check our list of data-driven web crawlers and contact us to find the right vendor:
This article was drafted by former AIMultiple industry analyst Rijja Younus.

Comments
Your email address will not be published. All fields are required.