Use Web Scrapers & Proxies to Protect Your Brand in 2024
With the rise of digitization and e-commerce, companies might not always be aware of infringements, or brand protection tools that are at their disposal. That’s why we are providing a detailed guide on brand protection, different kinds of brand infringements (such as counterfeiting or patent theft), and brand protection tools, such as web scrapers and proxy servers.
What is brand protection?
Brand protection is the process, and set of actions, that a copyright owner takes to prevent third parties from making unauthorized use of their intellectual property. Consequences of brand infringement include loss of revenue and tarnishing and diminishing of the brand’s value.
What are the different types of brand infringement?
Counterfeiting
Counterfeiting is the manufacture or distribution of goods under your brand name or intellectual property rights without your consent. Counterfeiting can take the form of imitations of your product or genuine counterfeits that are indistinguishable from the original product.

Image Source: Complex
Copyright infringement
Copyright infringement is the unauthorized copying, distribution, or display of your copyrighted works. Copyright extends to many areas, including literary works, videos, images, sound recordings, paintings, etc.
Trademark infringement
Trademark infringement occurs when another person or business uses a word, phrase, symbol, or design another business uses to distinguish its goods or services from others in the marketplace. In wine-making, for example, the word “Champagne” is a trademark of the region in France of the same name that produces the famous bubbly beverages. All other sparkling wine producers in the world are not allowed to call their products “Champagne,” even if they have the same specifications.
Patent theft
Patent theft is the act of someone else making or selling your patented product without your permission.
Design infringement
Design infringement is similar to patent infringement, with the only difference being the design that’s getting stolen. In the fashion industry, this is a prevalent issue.
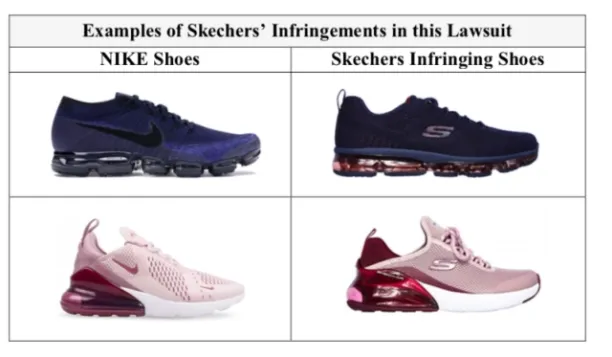
Image Source: Yahoo Finance
How can brand infringement happen and how can businesses tackle it?
In the online world, it has become easier than ever to infringe on brands. This can be done in the following ways:
Rogue/copycat websites
They are exactly what they sound like: Websites that imitate a brand’s official website, only with a subtly-altered URL. This is done to give the appearance of authenticity while selling fake products or services. These websites come in three forms:
- Those whose addresses contain a deliberate and clever typo, such as “Twiter” instead of “Twitter.”
- Those that mimic the spelling of the legitimate website, but are registered in another country, as in Twitter.com.sw.
- And those that create a duplicate of your website in your own home market. (Imagine a clone of the Angry Birds website in Finland itself!)
Recommendation: Use web scrapers integrated with proxies to be able to identify fake websites or unauthorized sellers that might be illegally profiting off of your products. Most of these websites are scattered around the world, and whether you are manually surfing the web or leveraging a web scraping tool, your access to the specific country’s IP might be restricted. Web scrapers that take advantage of proxies workaround that issue.
See our guide on different proxy server types to learn how they differ from one another in which ways.
Impersonation
When it comes to impersonating a brand, it usually involves social media impersonation and phishing websites. That is when fake accounts, under the guidance of your official brand, try to lure customers to fraudulent websites to sell them fake goods or collect their personal information for malicious intentions.
- Recommendation: Maintain a strong social media presence and report unofficial social media accounts to the moderators. For identifying fraudulent and phishing websites, invest in fraud protection software that helps e-commerce businesses to detect and prevent fraud-related activities.
For more on web scraping
Although web scraping is popular in e-commerce and security, it also has other uses cases:
- Top 18 Web Scraping Applications & Use Cases
- Web Scraping in Real Estate: Top 5 Use Cases & Data Sources
- Guide to Web Scraping in e-Commerce: Use Cases & Challenges
And because RPA is another tool at your disposal to protect your brand, we have prepared the Ultimate Guide on RPA for Cybersecurity with Top 7 Use Cases for you to read.
And we will help you through the process:

Cem has been the principal analyst at AIMultiple since 2017. AIMultiple informs hundreds of thousands of businesses (as per similarWeb) including 60% of Fortune 500 every month.
Cem's work has been cited by leading global publications including Business Insider, Forbes, Washington Post, global firms like Deloitte, HPE, NGOs like World Economic Forum and supranational organizations like European Commission. You can see more reputable companies and media that referenced AIMultiple.
Throughout his career, Cem served as a tech consultant, tech buyer and tech entrepreneur. He advised businesses on their enterprise software, automation, cloud, AI / ML and other technology related decisions at McKinsey & Company and Altman Solon for more than a decade. He also published a McKinsey report on digitalization.
He led technology strategy and procurement of a telco while reporting to the CEO. He has also led commercial growth of deep tech company Hypatos that reached a 7 digit annual recurring revenue and a 9 digit valuation from 0 within 2 years. Cem's work in Hypatos was covered by leading technology publications like TechCrunch and Business Insider.
Cem regularly speaks at international technology conferences. He graduated from Bogazici University as a computer engineer and holds an MBA from Columbia Business School.
To stay up-to-date on B2B tech & accelerate your enterprise:
Follow on

Comments
Your email address will not be published. All fields are required.