Affiliate Fraud: 6 Common Techniques & Best Practices in 2024
Affiliate marketing is a great way for businesses to generate leads and increase revenue. However, cyberattacks such as affiliate fraud pose a risk to companies in online sectors such as travel, retail, and finance. Marketers lost around $1.41 billion in 2020 due to affiliate fraud. Businesses that generate revenue through affiliate links must protect their websites from fraudsters to avoid wasting their advertising budget.
This article explains what affiliate fraud is, the 6 most common affiliate fraud techniques, and 3 best practices for preventing affiliate fraud.
What is affiliate fraud?
Affiliate fraud is a type of ad fraud that refers to any deceitful attempt to obtain unearned commissions from an affiliate marketing program.
The 6 most common techniques of affiliate fraud
1. Click fraud
Click fraud occurs in pay-per-click (PPC) online advertising. Websites that post the ads are paid based on the number of clicks generated by an advertisement. Click fraud is using a bot or a human to generate fake traffic on websites to generate unearned revenue.
Click fraud can be carried out by low-wage workers or robots. A person or a bot repeatedly clicks on an ad to generate large-scale traffic. Bot traffic can be easily identified by tracking visitors’ activities and behaviors across web pages. Some signs that can help you detect click fraud include:
- A high amount of clicks,
- Low conversion rate,
- Abnormal click-to-install time (CTIT)
However, fraudsters are likely to be aware of web-tracking technologies and use VPNs or constantly route their IP addresses to avoid revealing their identity.
2. Cookie stuffing
Cookie-stuffing, also known as cookie dropping, is an illegitimate affiliate marketing technique in which websites access users’ browser information by dropping invisible cookies into their browsers without their permission. Pop-ups, javaScript, browser extensions, images, and stylesheets plugins are common cookie-stuffing techniques.
Websites that run an affiliate program pay affiliates a commission for introducing and sending visitors to their website via a link or advertisement. Fraudulent affiliates use cookie-stuffing methods to make the website believe that they have directed users to the target affiliate site to gain unearned commission. For example, when a user visits a website, fraudsters drop malicious cookies onto visitors’ browsers from an unrelated website without their knowledge to steal commission.
3. Typosquatting
A typosquatting attack, also known as a URL hijacking or fake URL, occurs when a user accidentally enters an incorrect website address into the browser’s address bar. If the typo domain is purchased by typosquatters, you will be directed to a malicious website. Typosquatters guess the most likely typos and misspellings of popular website domains and purchase those typo domains for different reasons, such as selling the domain back to the legitimate website owner, ruining brand reputation, and earning commissions from the legitimate website’s affiliate program.
4. Chargeback Fraud
Chargeback fraud is the reversal of money from the cardholder’s bank account after receiving the purchased goods or services. Consumers can request chargebacks for various reasons, including card fraud, defective/damaged products, unauthorized payments, etc. Chargeback fraud is mostly done in three different ways:
- Friendly fraud occurs when a customer makes an honest mistake – e.g., a family member purchasing with a shared card without the knowledge of the cardholder.
- Criminal fraud occurs when an unauthorized person purchases goods and services using stolen credit card numbers without the cardholder’s permission.
- Merchant error refers to any problem that arises on the part of merchants, such as shipping the incorrect item or incorrect billing descriptions.
5. Malicious adware
Adware is a combination of advertisement and software. Websites place malicious adware on visitors’ devices without their permission. Affiliates use malicious adware to display advertisements on users’ devices and redirect users to the advertising website through a specific link while browsing the web. A program or app you want to install on your device may contain hidden malicious adware; when installing a program, ensure the web source is trustworthy.
6. SDK Spoofing
Software development kit (SDK) spoofing is a method used by fraudsters to create fake installs that appear legitimate to earn commissions. Fraudsters use tracking methods to monitor users’ activities and collect real device data to generate simulated ad clicks and traffic.
3 ways to prevent affiliate fraud
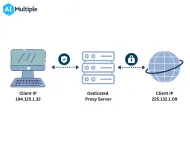
1. Proxy servers: make sure ads appear on the intended location
As an affiliate marketer, you must ensure that the ad is displayed on a safe platform, subject to human traffic, and seen by the desired audience. You can utilize proxy servers to test your localized affiliate content in multiple locations. Residential proxies are the best option to bypass geo-blocks and check ads are not shown at an undesired placement. Unlike datacenter proxies, residential proxies assign real IP addresses to users provided by an ISP (Internet Service Providers).
2. Browser fingerprinting: identify website visitors
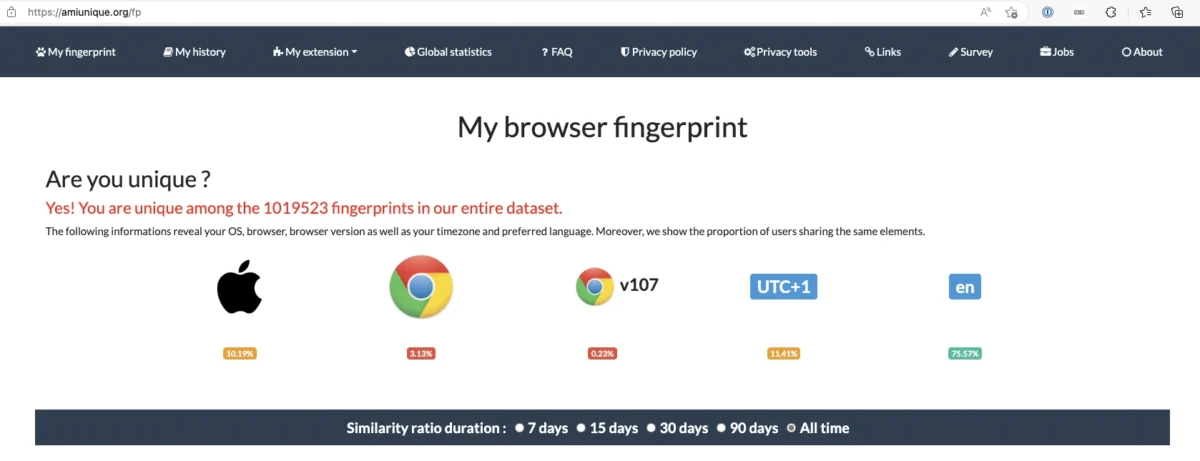
Browser fingerprinting allows website owners to track the activities and behaviors of online users. It enables websites to traffic that comes from non-human sources, such as bots, based on visitors’ behaviors such as session duration, request frequency, repeated pageviews from the same IP address, etc.
Websites can gather information about their visitors’ devices using browser fingerprint technology, including time zone, preferred language, browser type, installed plugins, user agent (see Figure 1). Data collected from the user’s device can be used to detect and block any suspicious user activity to protect website content from any fraudulent activity.
3. Tracking Affiliate Links
Websites can detect fraudulent activities by regularly monitoring affiliate link traffic. You can automatically track affiliate link clicks on your websites by using an analytics tool like Google Analytics or Google Tag Manager. When a specific event occurs on one of your affiliate links, analytics tools track and record it. For example, when someone clicks an affiliate link, you can see how many times affiliate links were clicked on a particular web page. When an unrealistic amount of clicks is attributed to a single IP address, you can distinguish the suspicious transaction based on your regular analytics patterns.
Also, don’t forget to check out our sortable/filterable list of proxy service / server.
For guidance to choose the right tool, reach out to us:
External Links
- 1. Coppinger, Kerry (May 31, 2022). “Affiliate marketing fraud now a $3.4 Billion problem, New Study Finds“. PRNewswire. Retrieved November 17, 2022.


Comments
Your email address will not be published. All fields are required.